Introduction
Web applications power nearly every aspect of modern business. From customer portals to internal management systems, these digital tools handle sensitive data and critical operations daily. Yet many businesses treat security as an afterthought, only addressing vulnerabilities after a breach occurs.
The statistics paint a sobering picture. Cyberattacks on web applications increased by 67% in recent years, with the average data breach costing businesses $4.45 million. Small and medium-sized businesses aren't exempt from these threats. In fact, they're often targeted precisely because attackers assume they have weaker defenses.
The good news? Most web application security breaches are preventable. Understanding the fundamentals of web app security and implementing proven best practices can dramatically reduce your risk exposure. You don't need a massive IT department or unlimited budget to protect your digital assets effectively.
This guide covers everything you need to know about securing your web applications. We'll explore common threats, essential security practices, and practical tools you can implement today. Whether you're launching a new application or auditing an existing one, you'll gain actionable insights to strengthen your security posture.
Think of web app security as building a house. You wouldn't construct walls without a solid foundation, and you wouldn't leave doors unlocked once you move in. The same principle applies to your digital presence. Security must be integrated from the ground up and maintained continuously.
Let's dive into the essential considerations that will help you protect your business, your customers, and your reputation in an increasingly connected world.
Understanding Web App Security Fundamentals

Web app security encompasses all measures taken to protect web-based applications from threats that could compromise data, functionality, or user privacy. At its core, it's about creating multiple layers of defense that work together to prevent unauthorized access and malicious activities.
The fundamental components of web app security include authentication (verifying user identity), authorization (controlling access to resources), data protection (encrypting sensitive information), and input validation (ensuring data integrity). These elements work in concert to create a secure environment where legitimate users can interact with your application while keeping threats at bay.
How Web Security Differs from General Cybersecurity
While general cybersecurity covers all aspects of digital protection, web app security focuses specifically on the unique vulnerabilities of internet-facing applications. Traditional cybersecurity might involve firewalls and antivirus software protecting a network perimeter. Web app security, however, deals with application-level threats that can bypass these traditional defenses.
Web applications are inherently more exposed than internal systems. They're designed to be accessible from anywhere, which means they're constantly under scrutiny from potential attackers. A single vulnerability in your application code can provide an entry point, regardless of how robust your network security might be.
This distinction matters because it requires a different mindset. You can't simply rely on perimeter defenses. Security must be built into the application itself, from the database queries to the user interface.
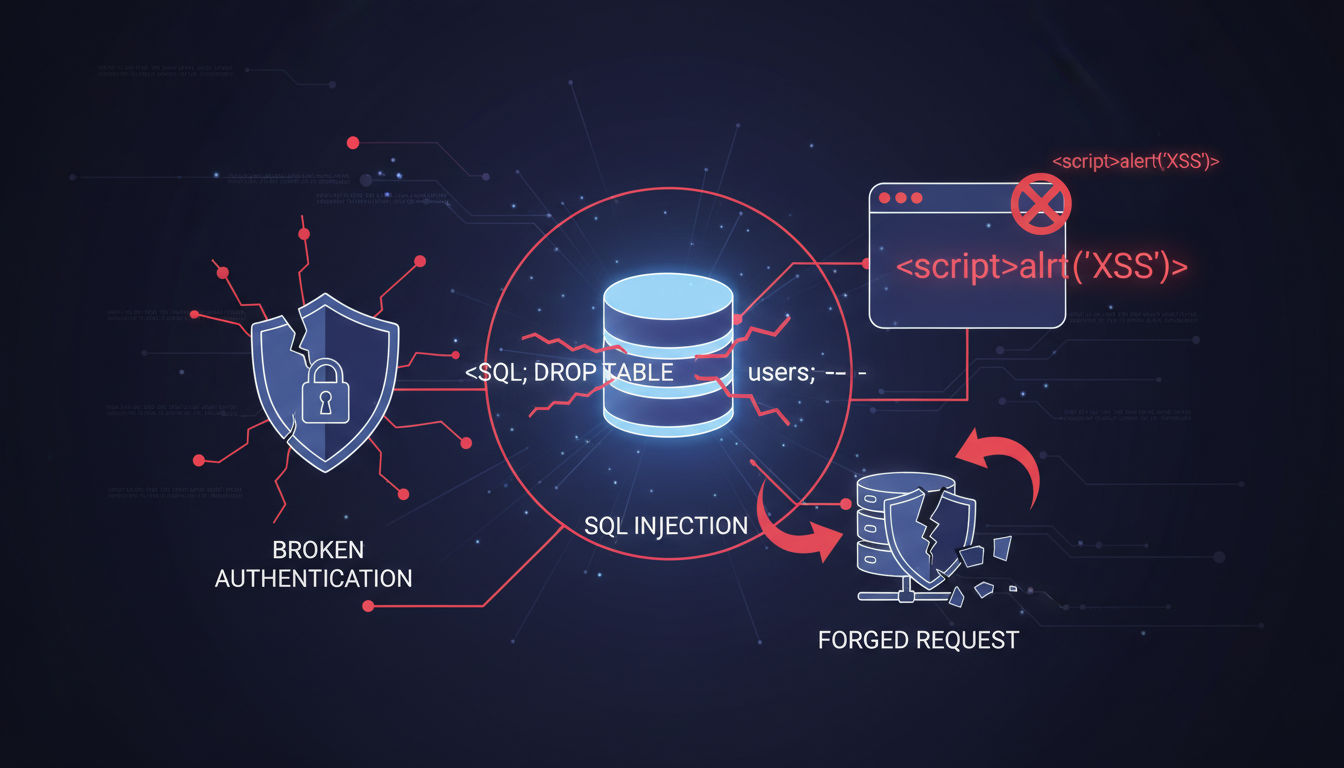
Common Vulnerabilities in Modern Applications
Modern web applications face numerous vulnerabilities, but certain patterns emerge consistently. Input validation issues allow attackers to inject malicious code or commands. Authentication weaknesses let unauthorized users gain access. Session management flaws enable attackers to hijack legitimate user sessions.
Configuration errors represent another major vulnerability category. Default settings, exposed administrative interfaces, and verbose error messages can all provide attackers with valuable information. Many businesses overlook these seemingly minor details until they become major problems.
Third-party dependencies introduce additional risk. The average web application uses dozens of external libraries and frameworks. Each one represents a potential vulnerability if not properly maintained and updated.
The Real Cost of Security Breaches
Beyond the immediate financial impact, security breaches damage customer trust and brand reputation in ways that persist long after the incident is resolved. A Montreal-based e-commerce company we consulted with lost 40% of their customer base after a data breach exposed payment information. The technical fix took weeks, but rebuilding trust took years.
Regulatory penalties compound these costs. GDPR, PIPEDA, and other privacy regulations impose significant fines for inadequate data protection. Healthcare and financial services face even stricter requirements with potentially severe consequences for non-compliance.
The operational disruption from a security incident often exceeds the direct costs. Systems go offline, teams scramble to contain the damage, and normal business operations grind to a halt. For businesses operating on tight margins, even a brief disruption can prove catastrophic.
Critical Security Best Practices for Web Applications

Implementing robust security practices doesn't require a complete application overhaul. Strategic improvements in key areas can dramatically enhance your security posture. Let's explore the practices that deliver the most significant protection for your investment.
Implementing Secure Authentication and Authorization
Authentication forms your first line of defense. Multi-factor authentication (MFA) should be standard, not optional. Even if passwords are compromised, MFA provides an additional barrier that stops most unauthorized access attempts.
Password policies matter more than many businesses realize. Requiring strong passwords isn't about making life difficult for users. It's about preventing the most common attack vector. Enforce minimum length requirements, complexity rules, and regular password updates. Consider implementing passwordless authentication methods like biometrics or hardware tokens for sensitive applications.
Authorization controls what authenticated users can access. Implement the principle of least privilege, giving users only the permissions they absolutely need. Role-based access control (RBAC) simplifies this process by grouping permissions into logical roles rather than managing individual user permissions.
Session management deserves special attention. Generate cryptographically secure session tokens, implement appropriate timeout periods, and ensure sessions are properly terminated upon logout. Never transmit session identifiers in URLs where they can be easily intercepted or logged.
Data Encryption: Protecting Information Everywhere
Encryption protects your data both in transit and at rest. For data in transit, HTTPS is non-negotiable. Transport Layer Security (TLS) encrypts all communication between users and your application, preventing eavesdropping and man-in-the-middle attacks.
Data at rest encryption protects stored information. This includes databases, file systems, and backup storage. Even if attackers gain physical access to your servers or steal backup media, properly encrypted data remains unreadable without the decryption keys.
Key management represents a critical component often overlooked. Store encryption keys separately from encrypted data, rotate keys regularly, and implement strict access controls. Consider using hardware security modules (HSMs) or cloud-based key management services for sensitive applications.
Don't forget about data in use. Memory scraping attacks can extract sensitive information from application memory during processing. While more complex to address, techniques like application-level encryption and secure enclaves provide additional protection for highly sensitive operations.
Regular Security Audits and Vulnerability Assessments
Security isn't a one-time project. Regular assessments identify new vulnerabilities before attackers exploit them. Schedule comprehensive security audits at least quarterly, with more frequent assessments for applications handling sensitive data.
Automated vulnerability scanners provide continuous monitoring, flagging common security issues as they emerge. These tools check for known vulnerabilities in your code, dependencies, and configurations. However, automated tools can't catch everything. They complement but don't replace manual security reviews.
Penetration testing simulates real-world attacks to identify weaknesses that might not appear in standard assessments. Engage qualified security professionals to attempt breaking into your application using the same techniques actual attackers would employ. The insights gained from these exercises prove invaluable.
Bug bounty programs leverage the security community to identify vulnerabilities. Offering rewards for responsibly disclosed security issues often costs less than a single breach while providing continuous security testing from diverse perspectives.
Secure Coding Practices and Code Reviews
Security starts with how your application is built. Developers must understand common vulnerabilities and how to prevent them. Input validation, output encoding, and parameterized queries should be standard practices, not special considerations.
Quick question
Want to turn this into a real plan?
If you want expert help with strategy, design, development, marketing, or automation — we’ll recommend the fastest path forward for your goals.
Code reviews catch security issues before they reach production. Implement mandatory peer reviews for all code changes, with specific attention to security implications. Consider using static application security testing (SAST) tools that analyze source code for potential vulnerabilities during development.
Establish secure coding standards for your team. Document approved libraries, frameworks, and coding patterns. Provide examples of secure implementations for common scenarios like user authentication, data validation, and error handling.
Training keeps security knowledge current. The threat landscape evolves constantly, with new attack techniques emerging regularly. Invest in ongoing security training for your development team, ensuring they stay informed about current best practices and emerging threats.
Keeping Software and Dependencies Updated
Outdated software represents one of the easiest attack vectors to exploit. Attackers actively scan for known vulnerabilities in popular frameworks and libraries. Once a vulnerability is disclosed publicly, you have a limited window to patch before automated attacks begin.
Establish a patch management process that prioritizes security updates. Critical security patches should be tested and deployed within days, not weeks or months. Balance the need for stability testing with the urgency of addressing known vulnerabilities.
Dependency management tools help track the libraries and frameworks your application uses. These tools alert you when vulnerabilities are discovered in your dependencies, enabling proactive updates before exploitation occurs.
Consider the entire stack when planning updates. Web servers, database systems, operating systems, and even hardware firmware all require regular updates. A vulnerability at any layer can compromise your entire application.
Common Web Application Security Threats
Understanding specific threats helps you prioritize defenses and recognize attacks in progress. While the threat landscape constantly evolves, certain attack patterns remain consistently prevalent and dangerous.
SQL Injection Attacks
SQL injection remains one of the most devastating web application vulnerabilities. Attackers insert malicious SQL code into input fields, manipulating database queries to access, modify, or delete data. A successful SQL injection can expose entire databases, including customer information, financial records, and authentication credentials.
The attack works by exploiting poor input validation. When applications directly concatenate user input into SQL queries, attackers can craft input that changes the query's logic. For example, entering ' OR '1'='1 in a login form might bypass authentication entirely.
Prevention requires parameterized queries or prepared statements. These techniques separate SQL code from data, ensuring user input is treated as data rather than executable code. Modern frameworks provide built-in protection, but developers must use these features correctly.
Real-world impacts are severe. A retail client we worked with discovered their legacy application was vulnerable to SQL injection. Before addressing the issue, attackers had already extracted customer data from several months of transactions. The incident resulted in regulatory fines, legal costs, and significant reputation damage.
Cross-Site Scripting (XSS)
Cross-site scripting allows attackers to inject malicious scripts into web pages viewed by other users. When victims load the compromised page, the malicious script executes in their browser, potentially stealing session cookies, capturing keystrokes, or redirecting users to phishing sites.
XSS comes in three main varieties. Stored XSS permanently embeds malicious scripts in the application's database. Reflected XSS tricks users into clicking links containing malicious code. DOM-based XSS manipulates the browser's Document Object Model to execute attacks entirely client-side.
The vulnerability stems from insufficient output encoding. When applications display user-generated content without properly sanitizing it, embedded scripts execute as if they were part of the legitimate application. Comments sections, user profiles, and search results are common attack vectors.
Prevention requires encoding all user-generated content before displaying it. Convert special characters like <, >, and " into their HTML entity equivalents. Implement Content Security Policy (CSP) headers that restrict which scripts can execute on your pages.
Cross-Site Request Forgery (CSRF)
CSRF attacks trick authenticated users into performing unintended actions. Attackers craft malicious requests that appear to come from legitimate users, exploiting the trust your application places in authenticated sessions. Users might unknowingly transfer funds, change passwords, or modify account settings.
The attack exploits how browsers automatically include credentials with requests. When a user is logged into your application and visits a malicious site, that site can trigger requests to your application. Your application sees valid session cookies and processes the request as legitimate.
Anti-CSRF tokens provide effective protection. Generate unique, unpredictable tokens for each session or request. Include these tokens in forms and AJAX requests, then validate them server-side before processing sensitive actions. Requests without valid tokens are rejected.
SameSite cookie attributes offer additional protection. Setting cookies to SameSite=Strict or SameSite=Lax prevents browsers from sending them with cross-origin requests, breaking the attack chain. This simple configuration change provides significant security improvement with minimal implementation effort.
Broken Authentication and Session Management
Authentication and session management flaws let attackers impersonate legitimate users. Weak password requirements, predictable session tokens, and improper session handling create opportunities for unauthorized access. Once attackers gain access, they can perform any action the compromised account is authorized to do.
Common issues include session fixation, where attackers force users to use predetermined session identifiers. Session hijacking intercepts valid session tokens through network sniffing or XSS attacks. Credential stuffing uses stolen username-password pairs from other breaches to gain access.
Account enumeration allows attackers to identify valid usernames. Different error messages for invalid usernames versus incorrect passwords provide valuable reconnaissance information. Login pages should return generic error messages that don't reveal whether the username exists.
Implementing proper session management prevents many attacks. Regenerate session identifiers after authentication. Implement absolute and idle timeouts. Secure session cookies with HttpOnly and Secure flags. Provide users with visibility into active sessions and the ability to terminate them remotely.
Security Misconfigurations
Misconfigurations represent one of the most common yet preventable vulnerabilities. Default credentials, unnecessary services, verbose error messages, and improper permissions all create security gaps. Attackers actively scan for these common mistakes, often using automated tools to identify vulnerable systems.
Default configurations prioritize ease of setup over security. Database servers with default passwords, administrative interfaces accessible without authentication, and development features enabled in production all provide easy entry points. Attackers maintain databases of default credentials and known misconfigurations.
Overly permissive CORS policies allow unauthorized domains to interact with your application. Directory listing exposes file structures and potentially sensitive documents. Unpatched vulnerabilities in server software provide known attack vectors. Each misconfiguration compounds your risk.
Prevention requires systematic hardening. Follow security benchmarks like CIS Controls or OWASP guidelines. Implement configuration management to ensure consistent, secure settings across all environments. Regularly audit configurations, especially after updates or changes. Automated configuration scanning tools help identify deviations from security baselines.
Application Security Tools and Technologies

The right tools amplify your security efforts, providing automated protection and continuous monitoring. While tools can't replace sound security practices, they significantly enhance your ability to detect and prevent attacks at scale.
Web Application Firewalls (WAF)
Web application firewalls filter and monitor HTTP traffic between your application and users. Unlike traditional network firewalls that operate at the network layer, WAFs understand application-layer protocols and can detect sophisticated attacks targeting application logic.
WAFs protect against common attacks like SQL injection, XSS, and CSRF by analyzing request patterns and blocking suspicious traffic. They use rule sets based on known attack signatures and can be customized with rules specific to your application. Modern WAFs also employ machine learning to identify anomalous behavior.
Cloud-based WAFs offer particular advantages for businesses without dedicated security teams. Services like Cloudflare, AWS WAF, and Azure Application Gateway provide enterprise-grade protection with minimal configuration. They also offer DDoS protection and content delivery network (CDN) capabilities.
Implementation requires careful tuning. Overly aggressive rules create false positives that block legitimate users. Too lenient, and attacks slip through. Start with monitoring mode to understand normal traffic patterns before enabling blocking. Regularly review and adjust rules based on your specific application behavior.
Security Testing Tools and Scanners
Automated security scanners identify vulnerabilities in your application code, configurations, and dependencies. These tools perform thousands of tests in minutes, checking for known vulnerabilities and security misconfigurations that might take security professionals hours to identify manually.
Dynamic Application Security Testing (DAST) tools scan running applications, simulating attacks to identify vulnerabilities. They test applications as black boxes, just as attackers would, without requiring access to source code. Popular tools include OWASP ZAP, Burp Suite, and Acunetix.
Static Application Security Testing (SAST) tools analyze source code to identify security flaws before deployment. They catch issues like SQL injection vulnerabilities, hardcoded credentials, and insecure cryptographic implementations during development. Integration with CI/CD pipelines enables continuous security testing.
Software Composition Analysis (SCA) tools track third-party dependencies and alert you to known vulnerabilities. They maintain databases of vulnerable library versions and can automatically suggest secure alternatives. This proves essential given the average application includes dozens of external dependencies.
Intrusion Detection and Prevention Systems
Intrusion Detection Systems (IDS) monitor network traffic and system activities for suspicious patterns. They alert security teams to potential attacks in progress, enabling rapid response before significant damage occurs. Intrusion Prevention Systems (IPS) take this further by automatically blocking detected threats.
Network-based systems monitor traffic across your entire infrastructure. Host-based systems focus on individual servers, monitoring file integrity, log files, and system calls. Combining both approaches provides comprehensive visibility into potential security incidents.
Modern systems employ behavioral analysis alongside signature-based detection. Rather than only identifying known attack patterns, they establish baselines of normal activity and flag deviations. This catches novel attacks that don't match existing signatures.
Effective implementation requires proper tuning and regular monitoring. False positives can overwhelm security teams, leading to alert fatigue where genuine threats get missed. Establish clear processes for investigating alerts and regularly review system effectiveness.
SSL/TLS Certificates and HTTPS Implementation
SSL/TLS certificates encrypt data transmitted between users and your application, preventing eavesdropping and tampering. HTTPS is no longer optional. Search engines penalize sites without it, browsers display warnings, and users increasingly expect the security it provides.
Certificate authorities (CAs) verify your identity and issue certificates. Let's Encrypt provides free certificates with automated renewal, removing cost barriers to HTTPS implementation. For businesses requiring extended validation or wildcard certificates, commercial CAs offer additional options.
Proper configuration matters as much as having a certificate. Disable outdated protocols like SSL 3.0 and TLS 1.0. Use strong cipher suites that provide forward secrecy. Implement HTTP Strict Transport Security (HSTS) headers to prevent protocol downgrade attacks.
Certificate management requires ongoing attention. Certificates expire, typically after 90 days for Let's Encrypt or one to two years for commercial certificates. Implement automated renewal processes to prevent lapses that could take your site offline or expose users to security warnings.
Security Information and Event Management (SIEM)
SIEM systems aggregate and analyze security data from across your infrastructure. They collect logs from web servers, databases, firewalls, and applications, correlating events to identify potential security incidents. This centralized visibility proves essential for detecting sophisticated attacks that span multiple systems.
Real-time analysis enables rapid threat detection. SIEM systems apply rules and machine learning algorithms to identify suspicious patterns as they occur. They can automatically trigger alerts or initiate response actions when specific conditions are met.
Compliance reporting represents another key benefit. SIEM systems maintain detailed audit trails and generate reports demonstrating compliance with regulations like GDPR, HIPAA, or PCI DSS. This documentation proves invaluable during audits or incident investigations.
Implementation complexity and cost once limited SIEM to large enterprises. Cloud-based SIEM solutions now make this technology accessible to smaller businesses. Services like Splunk Cloud, Microsoft Sentinel, and Google Chronicle offer scalable solutions without requiring significant infrastructure investment.
Building a Web Security Strategy for Your Business
Effective security requires more than implementing tools and technologies. A comprehensive strategy aligns security measures with business objectives, creates clear processes, and establishes accountability throughout your organization.
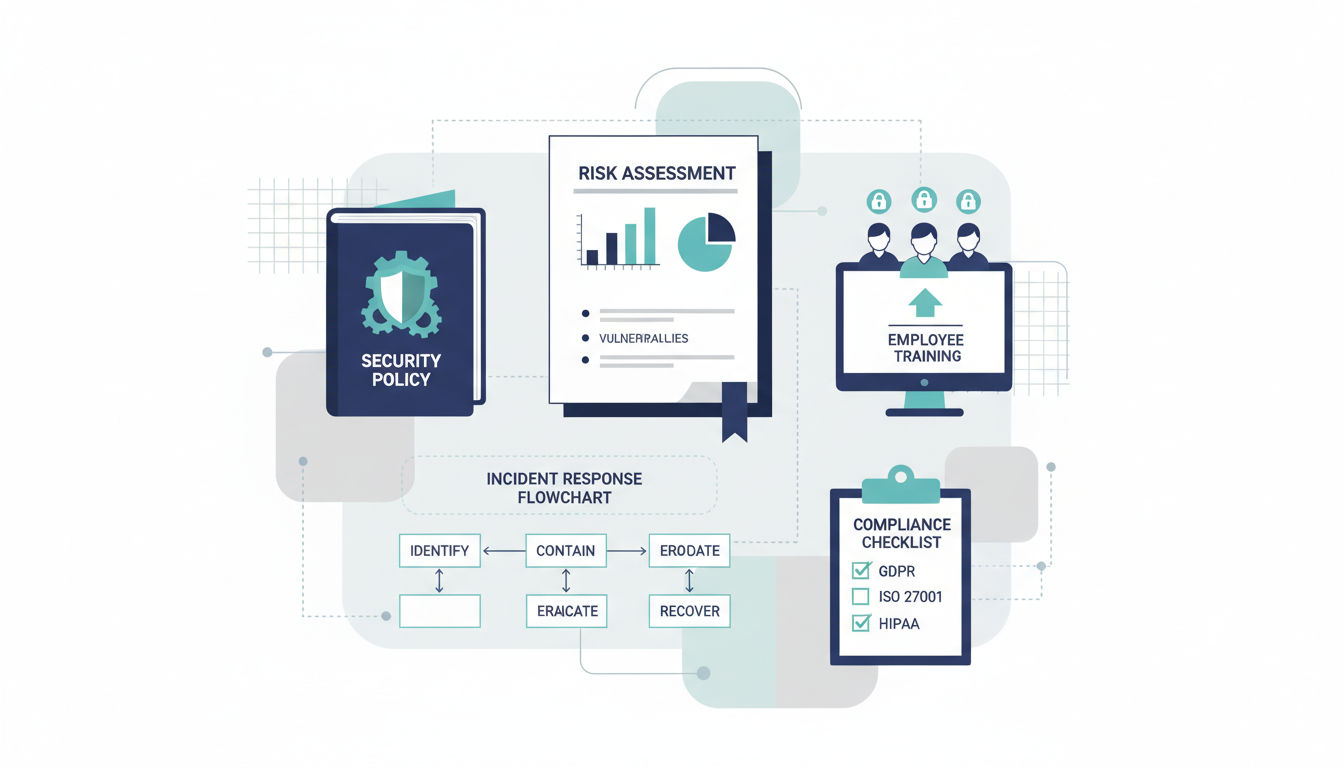
Conducting a Security Risk Assessment
Risk assessment identifies your most critical assets and the threats they face. Start by cataloging all web applications, the data they handle, and the business processes they support. Not all assets require the same level of protection. Customer payment data demands more stringent security than a public-facing blog.
Identify potential threats specific to your business. E-commerce sites face different risks than healthcare portals or internal business applications. Consider both external threats like hackers and insider threats from employees or contractors. Don't overlook physical security, social engineering, and supply chain risks.
Evaluate your current security posture honestly. Document existing controls, identify gaps, and assess the likelihood and potential impact of various threats. This analysis reveals where you're vulnerable and helps prioritize security investments for maximum risk reduction.
Quantifying risk helps justify security spending to stakeholders. Calculate potential losses from different scenarios, considering direct costs, regulatory fines, business disruption, and reputation damage. Compare these potential losses against the cost of preventive measures to build a compelling business case.
Developing Security Policies and Procedures
Written policies establish security expectations and requirements across your organization. They provide clear guidance for employees, contractors, and partners interacting with your systems. Without documented policies, security becomes inconsistent and dependent on individual judgment.
Access control policies define who can access what resources and under what circumstances. Password policies establish requirements for creating and managing credentials. Data handling policies specify how sensitive information should be stored, transmitted, and disposed of. Incident response procedures outline steps to take when security events occur.
Policies must be practical and enforceable. Overly restrictive policies that interfere with legitimate work get ignored or circumvented. Involve stakeholders from different departments when developing policies to ensure they address real business needs while maintaining appropriate security.
Regular policy reviews keep security requirements current. Technology changes, business processes evolve, and new threats emerge. Schedule annual policy reviews, with updates triggered by significant changes to your infrastructure, business model, or threat landscape.
Employee Training and Security Awareness
Employees represent both your greatest vulnerability and your strongest defense. Phishing attacks, weak passwords, and social engineering succeed because people make mistakes. Comprehensive security training reduces these human errors significantly.
Initial training should cover security basics: recognizing phishing attempts, creating strong passwords, handling sensitive data, and reporting suspicious activity. Make training relevant with examples specific to your industry and the roles employees perform. Generic, abstract training fails to engage or create lasting behavior change.
Ongoing awareness programs reinforce security concepts. Monthly security tips, simulated phishing exercises, and regular reminders keep security top of mind. Gamification and positive reinforcement prove more effective than punishment for security mistakes.
Role-specific training addresses the unique security responsibilities of different positions. Developers need secure coding training. Customer service representatives need social engineering awareness. Executives need to understand their role as high-value targets. Tailor training content to each audience for maximum effectiveness.
Incident Response Planning
Despite best efforts, security incidents occur. Incident response plans minimize damage by ensuring rapid, coordinated responses. Without a plan, teams waste critical time figuring out what to do while attackers maintain access or data continues leaking.
Your plan should define roles and responsibilities clearly. Who leads the response effort? Who communicates with customers, regulators, and media? Who handles technical remediation? Establish communication channels and escalation procedures before incidents occur.
Document specific procedures for different incident types. Data breaches require different responses than DDoS attacks or ransomware infections. Include contact information for key personnel, external security experts, legal counsel, and law enforcement. Maintain both digital and printed copies in case systems are compromised.
Next step
Ready for a quote and timeline?
Send a quick note with what you’re building, your deadline, and what success looks like — we’ll reply with clear next steps.
Regular testing validates your incident response plan. Tabletop exercises walk teams through hypothetical scenarios, identifying gaps in procedures or resources. Full-scale simulations test your ability to execute the plan under pressure. Update plans based on lessons learned from exercises and actual incidents.
Compliance Requirements and Industry Standards
Regulatory compliance isn't optional. PIPEDA governs personal information handling in Canada. Organizations operating in Europe must comply with GDPR. Industry-specific regulations like PCI DSS for payment processing or HIPAA for healthcare impose additional requirements.
Compliance frameworks provide structured approaches to security. ISO 27001 offers a comprehensive information security management system. NIST Cybersecurity Framework provides risk-based guidance. SOC 2 addresses security, availability, and confidentiality for service providers. Adopting recognized frameworks demonstrates commitment to security and facilitates customer trust.
Documentation proves essential for compliance. Maintain records of security policies, procedures, training completion, audit results, and incident responses. Regulators expect evidence that you're actively managing security, not just claiming compliance. At Vohrtech, we help businesses implement documentation systems that satisfy regulatory requirements without creating excessive administrative burden.
Compliance requirements evolve as regulations change and your business grows. Stay informed about regulatory updates affecting your industry. Consider engaging compliance specialists for complex requirements or high-risk industries. The cost of non-compliance far exceeds the investment in proper compliance programs.
Working with Professional Web Security Services
Many businesses lack the internal expertise or resources to implement comprehensive security programs. Professional security services fill this gap, providing specialized knowledge and ongoing support that would be difficult to maintain in-house.
When to Bring in Security Experts
Consider professional security services when launching new applications, especially those handling sensitive data. Building security in from the start costs far less than retrofitting security after deployment. Security experts help design architectures that are inherently more secure and identify potential vulnerabilities before they're coded into your application.
Existing applications benefit from professional security assessments. If your application hasn't undergone thorough security testing, or if it's been more than a year since the last assessment, engage security professionals for a comprehensive audit. They bring fresh perspectives and specialized knowledge that internal teams might miss.
After security incidents, professional help accelerates recovery and prevents recurrence. Security experts can contain breaches, identify how attackers gained access, and implement measures to prevent similar incidents. They also provide objective incident analysis that proves valuable for insurance claims and regulatory reporting.
Compliance requirements often necessitate external expertise. Achieving certifications like SOC 2 or PCI DSS compliance requires specialized knowledge of framework requirements and assessment procedures. Security consultants guide you through the process, helping avoid costly mistakes and delays.
How Web Design Agencies Can Integrate Security from the Start
Security should inform every phase of application development, not serve as a final checklist item. At Vohrtech, we integrate security considerations into our development process from initial planning through deployment and maintenance.
Threat modeling during the design phase identifies potential security issues before writing code. We analyze how users will interact with your application, what data flows through the system, and where vulnerabilities might emerge. This proactive approach prevents security problems rather than discovering them through testing or, worse, actual attacks.
Secure development practices include code reviews, automated security testing, and adherence to established security standards. We implement security controls as core features, not afterthoughts. Authentication, authorization, encryption, and input validation are built into the application architecture from day one.
Security testing occurs throughout development, not just before launch. Continuous integration pipelines include automated security scans that catch vulnerabilities as code is written. Manual penetration testing before deployment provides additional assurance that security controls function as intended.
Ongoing Security Maintenance and Monitoring
Security isn't a one-time project. Threats evolve, new vulnerabilities are discovered, and applications change over time. Ongoing maintenance ensures your security posture remains strong as your application and the threat landscape evolve.
Regular monitoring detects security issues before they become breaches. We implement logging and alerting systems that flag suspicious activities in real-time. Security information gets reviewed regularly, not just when problems occur. This proactive monitoring catches attacks in early stages when they're easier to contain.
Patch management keeps your application and infrastructure secure against known vulnerabilities. We track security updates for all components of your application stack and test and deploy critical patches promptly. This systematic approach prevents exploitation of publicly disclosed vulnerabilities.
Security retesting after significant changes ensures new features don't introduce vulnerabilities. Application updates, infrastructure changes, and integration of third-party services all warrant security review. We treat security as an ongoing process, not a one-time achievement.
Choosing the Right Security Partner
The right security partner understands both technical security and business needs. They communicate clearly without overwhelming you with jargon. They provide actionable recommendations, not just lists of vulnerabilities. Look for partners who take time to understand your business, risk tolerance, and budget constraints.
Experience in your industry matters. Healthcare applications face different security challenges than e-commerce sites or SaaS platforms. Partners familiar with your industry understand relevant compliance requirements and common threat vectors. They provide context-appropriate recommendations rather than generic advice.
Transparency and communication separate good security partners from mediocre ones. You should understand what services you're receiving, what they cost, and what results to expect. Regular reporting keeps you informed about your security posture and any issues requiring attention.
Consider the full scope of services offered. Comprehensive security requires multiple capabilities: assessment, implementation, monitoring, and incident response. Partners offering integrated services provide better coordination than cobbling together multiple vendors. If you're looking for a partner who understands the Montreal market while serving clients globally, reach out to discuss how we can help secure your web applications.
Conclusion
Web application security demands attention, investment, and ongoing commitment. The threats are real and constantly evolving. However, the steps needed to protect your applications are well understood and achievable for businesses of any size.
Start with the fundamentals: secure authentication, data encryption, regular updates, and security testing. These core practices prevent the vast majority of attacks. Build on this foundation with tools like web application firewalls, security scanners, and monitoring systems that provide automated protection and visibility.
Remember that security is a process, not a destination. Regular assessments, continuous monitoring, and prompt responses to emerging threats keep your applications secure over time. Employee training and clear security policies extend protection beyond technical controls to address the human elements of security.
Professional security services provide expertise and resources that many businesses struggle to maintain internally. Whether you're launching a new application or improving security for existing systems, partnering with experienced security professionals accelerates your progress and reduces risk.
The cost of implementing proper security measures pales in comparison to the potential impact of a breach. Beyond direct financial losses, consider the damage to customer trust, brand reputation, and business operations. Investing in security protects not just your data and systems, but your business's future.
Take action today. Assess your current security posture, identify your most critical vulnerabilities, and implement improvements systematically. Every security enhancement reduces your risk and strengthens your defense against threats. Your customers, partners, and stakeholders will thank you for taking their security seriously. Visit our projects page to see how we've helped businesses like yours build secure, reliable web applications that protect what matters most.
